Understanding PDF Encryption:
AES-256 vs RC4
Is your PDF protection just a facade? Dive deep into the mathematical reality of document security and learn why your tools must evolve in 2026.
Not all PDF protection is created equal. When you "add a password" to a PDF, you are actually instructing a piece of software to run a complex mathematical algorithm on your data. Depending on which algorithm you choose, your document is either an unhackable fortress or a flimsy screen door.
In this guide, we'll demystify the acronyms and explain why AES-256 is the non-negotiable gold standard for document security in 2026.
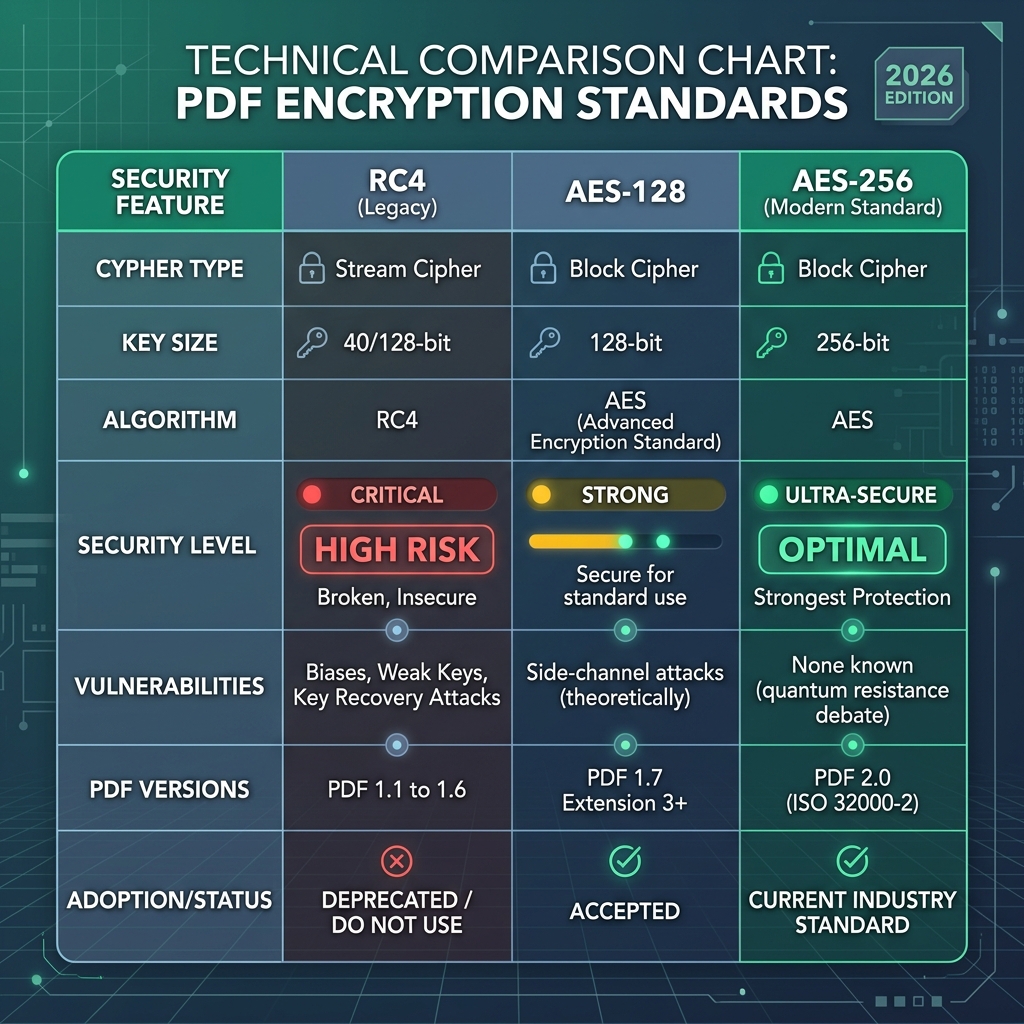
| Standard | Security Level | Vulnerability | Status |
|---|---|---|---|
| RC4 (40-bit) | 🔴 Critical Risk | Cracked in seconds | Obsolete |
| RC4 (128-bit) | 🟡 High Risk | Weak to "Bit-Flipping" | Deprecated |
| AES (128-bit) | 🟢 Good | None (known) | Acceptable |
| AES (256-bit) | 💎 Military Grade | Quantum Resistant | Recommended |
The Rise and Fall of RC4
RC4 (Rivest Cipher 4) was the dominant stream cipher for decades. It was fast and simple, which made it perfect for early PDF readers with limited processing power. However, as computational power grew, mathematical flaws in RC4 were exposed.
The Core Problem: RC4 generates a "keystream" that has subtle biases. These biases allow attackers to reconstruct your password by analyzing multiple versions of the same encrypted file. Today, an RC4-protected PDF can be cracked by standard consumer hardware in under a minute.
Why AES-256 is Unbreakable
The Advanced Encryption Standard (AES) is a symmetric block cipher that processes data in 128-bit blocks using keys of 128, 192, or 256 bits. It's the standard chosen by the U.S. government to protect classified information.
The "Brute Force" Reality: To crack a 256-bit AES key through brute force (trying every combination), a supercomputer would need roughly 1.1 x 10^77 years. For context, the universe is only 1.4 x 10^10 years old. In 2026, AES-256 remains mathematically invincible.
How Raha Tools Implements Security
Most "online" password protectors are actually security risks themselves—they require you to send your unencrypted document to their server, where they encrypt it. This means they have a copy of your sensitive data in its raw form.
Raha Tools uses Client-Side Cryptography. When you use our Protect PDF Tool, the encryption happens inside your browser's WebAssembly engine. Your document never leaves your device in an unencrypted state. Your password is never sent to our servers. We provide the tools; you maintain the keys.
Military-Grade Protection
Encrypt your documents with zero-knowledge AES-256. 100% Private.
Secure My PDF NowSecurity FAQ
What is the difference between an 'Open Password' and a 'Permission Password'?
An **Open Password** prevents anyone from viewing the file without the code. A **Permission Password** (or Owner Password) allows viewing but restricts actions like printing, editing, or copying text.
Is it legal to use AES-256 for business contracts?
Yes. AES-256 is the industry standard for legally binding documents and is compliant with GDPR, HIPAA, and most international data protection laws.